My Multi-Server Homelab: The Full Architecture
Three VPSes. 30+ containers. One Tailscale mesh holding it all together. Here's every service, every connection, and how they talk to each other.
The Setup
- Main VPS (Hetzner) - Reverse proxy, DNS, auth, media, mail, everything else
- Transmission VPS (Hetzner) - Torrenting through Mullvad VPN
- OCI VPS (Oracle Cloud) - Media transcoding
All three servers are connected via Tailscale (100.x.x.x addresses). The Main VPS runs Traefik as the single public entry point for all web traffic across all servers. Authentik handles SSO for protected services. A Hetzner Storage Box is mounted on all servers for shared media storage.
Network Overview
How traffic flows from the internet through Traefik to services across all three servers.
Main VPS - All Services Behind Traefik
Every service on the main VPS is exposed through Traefik with automatic Let's Encrypt certificates.
Media Pipeline
The fully automated media acquisition and processing pipeline.
Authentication Flow
Authentik protects selected services via Traefik's forwardAuth middleware.
Cross-Server Management
Portainer on the main VPS manages all three servers via agents over Tailscale.
Service Breakdown
Networking & Security
- Traefik - Single entry point for all HTTP/HTTPS traffic. Handles TLS via Let's Encrypt, routes to local containers and remote servers via Tailscale IPs. Also routes Minecraft TCP traffic on :25565.
- Authentik - Full SSO stack with server, worker, LDAP provider, and a forward auth outpost on the main VPS. Protects Jellyfin and Transmission via Traefik's forwardAuth middleware.
- Technitium - DNS server accessible over Tailscale only (:53 bound to Tailscale IP). Logs to MariaDB.
- Tailscale - Mesh VPN connecting all three servers. Traefik uses Tailscale IPs to reverse proxy services on remote VPSes.
Media Automation
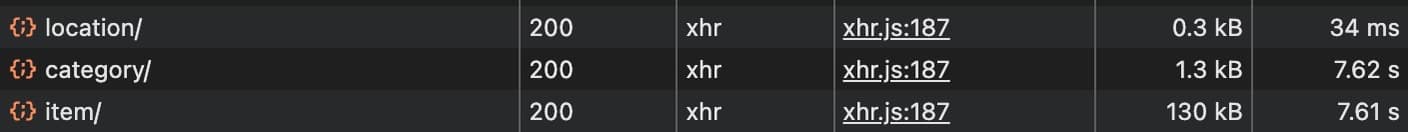
Requests flow through a fully automated pipeline: Jellyseerr (request UI) -> Sonarr/Radarr (library managers) -> Prowlarr (indexer) -> Byparr (CAPTCHA solving) -> Transmission (downloads via Mullvad VPN) -> Unmanic (transcoding) -> Jellyfin (streaming). All media lives on the Hetzner Storage Box mounted across servers.
Self-hosted Docker Mailserver handles SMTP/IMAP with SpamAssassin and Fail2ban. Roundcube provides webmail. Both ntfy and Kener route notifications through the mail server.
Everything Else
- Linkwarden - Bookmark manager with its own Postgres and Meilisearch instances
- PocketBase - Backend for side projects
- ntfy - Push notifications (powers the /ping page on this site)
- Kener - Status page at status.kanishksachdev.com
- Homepage - Dashboard at home.kanishksachdev.com
- Minecraft - Vanilla server, because why not
- Portainer - Manages all three servers via remote agents
- Cloud Commander - Web file manager for the storage box
Transmission VPS
Isolated server dedicated to torrenting. Gluetun wraps Transmission's traffic through a Mullvad WireGuard tunnel (Sweden exit). Traefik on the main VPS reverse proxies the web UI over Tailscale, protected by Authentik.
OCI VPS
Free-tier Oracle Cloud instance running an Unmanic worker node for distributed transcoding, mounting the shared storage box.